- Gemini could automatically run certain commands previously placed on a allowed list
- If a benign command was paired with a malicious, Gemini could perform it without warning
- Version 0.1.14 addresses the error so users need to update now
A security error in Google’s new Gemini CLI tool allowed threat players to target software developers with malware, even exfilter sensitive information from their devices, without ever knowing it.
Vulnerability was discovered by CyberSecurity researchers from Tracebit just days after the Gemini Cli was only launched on June 25, 2025.
Google released a solution with the version 0.1.14, which can now be downloaded.
Hiding the attack in plain sight
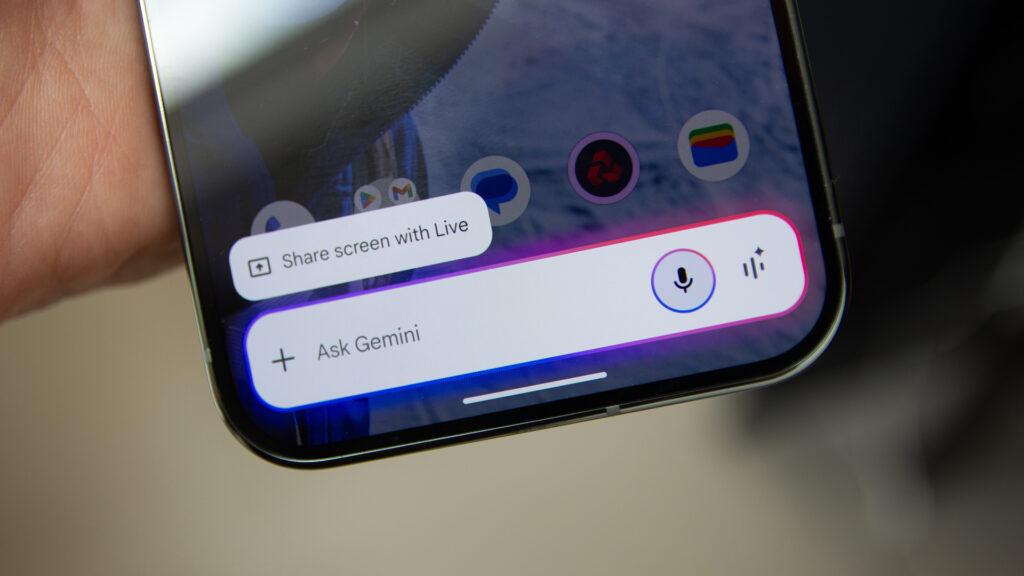
Gemini Cli is a tool that lets developers talk to Google’s AI (called Gemini) directly from the command line. It can understand code, make suggestions and even run commands on the user’s device.
The problem stems from the fact that Gemini could automatically run certain commands previously placed on a allowed list. According to Tracebit, there was a way to sneak hidden, malicious instructions in files that Gemini reads, like readme.md.
In a test, a seemingly harmless command was paired with a malicious, exfiltering sensitive information (such as system variables or credentials) for a third -party server.
Because Gemini thought it was just a trusted command, it didn’t warn the user or asked for approval. Tracebit also says the malicious command could be hidden using smart formatting, so users wouldn’t even see it happen.
“The malicious command could be anything (installing a remote shell, deleting files, etc.),” the researchers explained.
However, the attack is not so easy to pull off. It requires a small setup, including having a trusted command on the permitted list, but it can still be used to trick unsuspecting developers into running dangerous code.
Google has now patched the problem and if you are using Gemini Cli, be sure to update to version 0.1.14 or newer as soon as possible. Also, make sure not to run it on unknown or non -procedure code (unless you are in a secure test environment).
Via Bleeping computer