Google’s Quantum AI team said earlier this week that a future quantum computer could derive a private bitcoin key from a public key in about nine minutes. The number ricocheted across social media and spooked markets.
But what does this actually mean in practice?
Let’s start with how bitcoin transactions work. When you send bitcoin, your wallet signs the transaction with a private key, a secret number that proves you own the coins.
This signature also reveals your public key, a sharable address that is broadcast to the network and sits in a waiting pool called the mempool until a miner includes it in a block. On average, that confirmation takes about 10 minutes.
Your private key and public key are connected by a mathematical problem called the elliptic curve discrete logarithm problem. Classical computers can’t reverse that math in any useful time frame, while a sufficiently powerful future quantum computer running an algorithm called Shor’s could.
Here’s where the nine-minute part comes in. Google’s paper found that a quantum computer could be “primed” in advance by pre-computing the parts of the attack that do not depend on any specific public key.
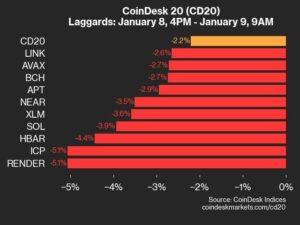
Once your public key appears in the mempool, the machine only needs about nine minutes to finish the job and derive your private key. Bitcoin’s average confirmation time is 10 minutes. This gives the attacker an approx. 41% chance of deriving your key and diverting your funds before the original transaction is confirmed.
Think of it as a thief spending hours building a universal safe-cracking machine (precomputation). The machine works for any safe, but each time a new safe appears, it only needs a few final adjustments – and the last step is the one that takes about nine minutes.
It is the mempool attack. That’s alarming, but requires a quantum computer that doesn’t exist yet. Google’s paper estimates that such a machine would need fewer than 500,000 physical qubits. Today’s largest quantum processors have about 1,000.
The bigger and more immediate concern is the 6.9 million bitcoins, about a third of the total supply, already sitting in wallets where the public key has been permanently exposed.
This includes early bitcoin addresses from the early years of the network that used a format called pay-to-public-key, where the public key is visible on the blockchain by default. It also includes any wallet that has reused an address, as spending from an address reveals the public key of all remaining funds.
These coins do not need the nine-minute run. An attacker with a sufficiently powerful quantum computer could crack them at will and work through exposed keys one by one without any time pressure.
Bitcoin’s 2021 Taproot upgrade made this worse, as CoinDesk reported earlier Tuesday. Taproot changed how addresses work so that public keys are visible on-chain by default, inadvertently widening the pool of wallets that would be vulnerable to a future quantum attack.
The bitcoin network itself would continue to run. Mining uses a different algorithm called SHA-256, which quantum computers cannot meaningfully speed up with current approaches. Blocks would still be produced.
The ledger would still exist. But if private keys can be derived from public keys, the ownership that makes bitcoin valuable is guaranteed to be broken down. Anyone with exposed keys is at risk of theft, and institutional trust in the network’s security model breaks down.
The fix is post-quantum cryptography, which replaces the vulnerable math with algorithms that quantum computers can’t crack. Ethereum has spent eight years building against that migration. Bitcoin hasn’t even started.