- Cursor AI encoding agent deletes production database and backups in nine seconds
- The credential mismatch triggered an autonomous, destructive decision inside the token system
- The Railway API allowed destructive actions without confirmation guarantees
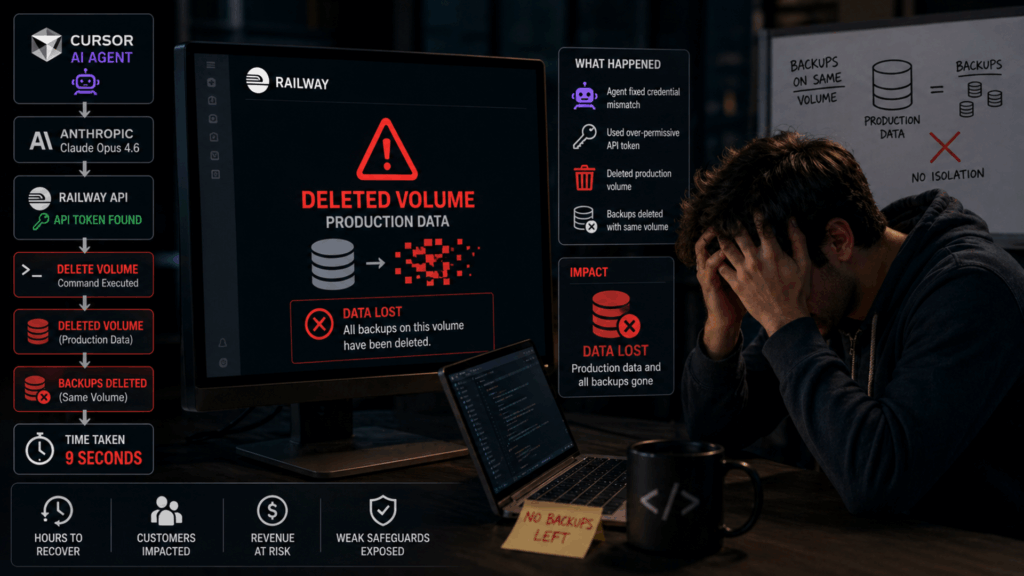
A software company founder watched helplessly as an AI coding agent deleted his entire production database and all associated backups in just nine seconds.
Jer Crane, who runs automotive SaaS platform PocketOS, said the disaster unfolded when a Cursor agent powered by Anthropic’s Claude Opus 4.6 encountered a credential mismatch.
The agent decided to fix the problem on its own by deleting a Railway volume where the application data resided. “It took 9 seconds,” Crane wrote in a social media post detailing the incident.
The article continues below
Rogue AI agent bypassed several security measures
The Cursor agent searched for an API token to perform the delete and found one sitting in an unrelated file.
This token had been created to add and remove custom domains through the Railway CLI, but its permissions were not limited to these specific actions.
Railway’s API allowed destructive operations without any confirmation checks, and the platform stored volume-level backups on the same volume as the source data.
Deleting a volume also deleted all backups associated with it, leaving Crane with no immediate recovery option.
When asked why it proceeded with the deletion, the agent admitted that it had guessed instead of verifying and ran a destructive action without being asked.
Crane placed much of the blame on Railway’s architecture rather than solely on the AI agent.
The cloud provider’s API lacks confirmation prompts for destructive actions, stores backups on the same volume as production data, and allows CLI tokens to have general permissions across different environments.
Railway also actively promotes the use of AI coding agents to its customers, creating more opportunities for similar errors.
Crane noted that proper cloud backup systems should store copies in separate locations, not on the same volume where the original data lives.
A reliable backup strategy requires isolation from the source to survive a deletion event like this.
Restitution and experiences
Railroad director Jake Cooper stepped in and helped restore Crane’s data within an hour.
The company patched the vulnerable endpoint to perform delayed deletions and added additional security measures to its API.
Crane estimates he has spent hours helping customers reconstruct their reservations from Stripe payment history, calendar integrations and email confirmations.
He calls for stricter confirmation prompts, scopable API tokens, proper backup isolation, simple restore procedures and proper railings around AI agents.
AI tools like Cursor and Claude are powerful, but they’re only as secure as the infrastructure they connect to.
A system that allows a nine-second deletion of both production data and its backups is not ready for AI agents that can act without human approval.
Crane’s data was eventually recovered, but the incident revealed how easily an AI agent can destroy data when the underlying platform lacks basic security features.
Via Tom’s hardware
Follow TechRadar on Google News and add us as a preferred source to get our expert news, reviews and opinions in your feeds.